Cobalt Strike is a benchmark red teaming tool ideal for adversary simulations, particularly those with a focus on post-exploitation exercises. Using its adaptable C2 framework and signature advanced payload, Beacon, security professionals can replicate the tactics, techniques, and procedures of real-world attackers for accurate assessments of organizational defenses.
Key Features
Flexibility
Cobalt Strike’s flexible Command and Control (C2) framework can be easily extended with personalized tools and techniques.
Post-Exploitation
With Beacon, Cobalt Strike’s signature payload, users can replicate the behavior of an advanced adversary, quickly expanding their foothold.
Arsenal Kit
Operators can use and tailor Cobalt Strike’s collection of tools, including:
– Sleep Mask Kit
– Mutator Kit- User-Defined Reflective Loaders
Covert Communication
Beacon provides several communication channels to reduce the risk of being identified.
Additionally, Malleable C2 profiles can be created to change network indicators.
Community
The Cobalt Strike Community Kit is a curated repository of over 100 user-built tools, continuously expanded with contributions from its active community to extend the framework’s capabilities.
Interoperability with OST
OST integrates directly with Cobalt Strike through BOFs and reflective DLL loading techniques, providing an OPSEC safe way to efficiently perform highly technical and difficult post-exploitation tasks.
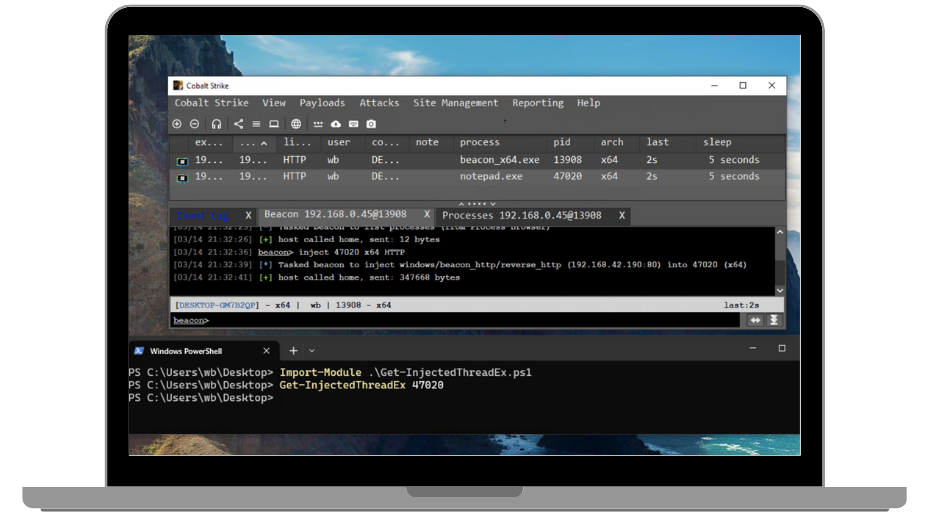
Cobalt Strike Demo
Get a guided walkthrough of Cobalt Strike to see Cobalt Strike’s capabilities in action and learn how to navigate this powerful adversary simulation solution.
Cobalt Strike Product Suites
Cobalt Strike can be further extended by pairing it with interoperable tools, Core Impact and Outflank Security Tooling. Additionally, suites include exclusive benefits unavailable with standalone product purchases: Access to Cobalt Strike Research Labs’ specialized tooling and Certified Operator training.
| Red Team Suite Cobalt Strike & Outflank Security Tooling (OST) Seamlessly integrate a leading post-exploitation framework with an advanced offensive security toolkit focused on obfuscation, enabling red teams to execute diverse tasks across the entire attack chain in order to rigorously test detection and response maturity. Learn More > Request a Quote > |
| Offensive Security Suite Cobalt Strike, Core Impact, & OST Safely evaluate infrastructures to create more resilient security strategies using automated pen testing, adaptive adversary simulation, and cutting edge evasion techniques to provide realistic threat emulations and validate defenses in high-security environments. Learn More > Request a Quote > |
Ready to see what Cobalt Strike can do for your organization?
Request a quote or try it for yourself to get started.